Go API: Authorization
This tutorial demonstrates how to add authorization to a Go API. We recommend that you log in to follow this quickstart with examples configured for your account.
I want to integrate with my app
15 minutesI want to explore a sample app
2 minutesGet a sample configured with your account settings or check it out on Github.
Configure Auth0 APIs
Create an API
In the APIs section of the Auth0 dashboard, click Create API. Provide a name and an identifier for your API, for example, https://quickstarts/api. You will use the identifier as an audience later, when you are configuring the Access Token verification. Leave the Signing Algorithm as RS256.
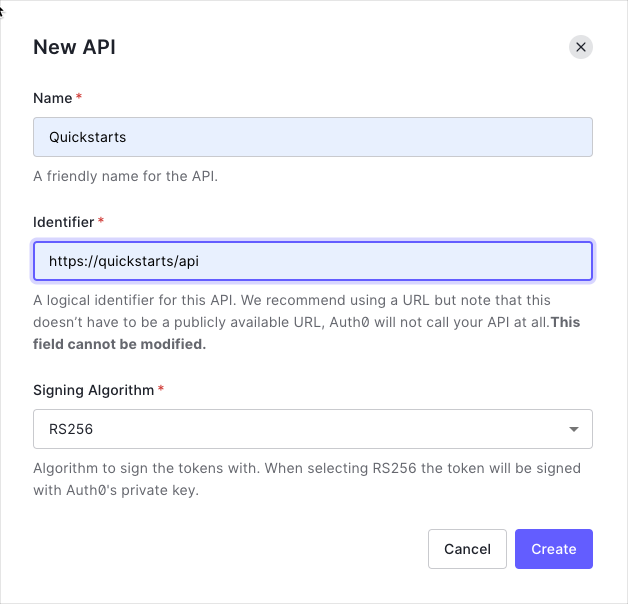
By default, your API uses RS256 as the algorithm for signing tokens. Since RS256 uses a private/public keypair, it verifies the tokens against the public key for your Auth0 account. The public key is in the JSON Web Key Set (JWKS) format, and can be accessed here.
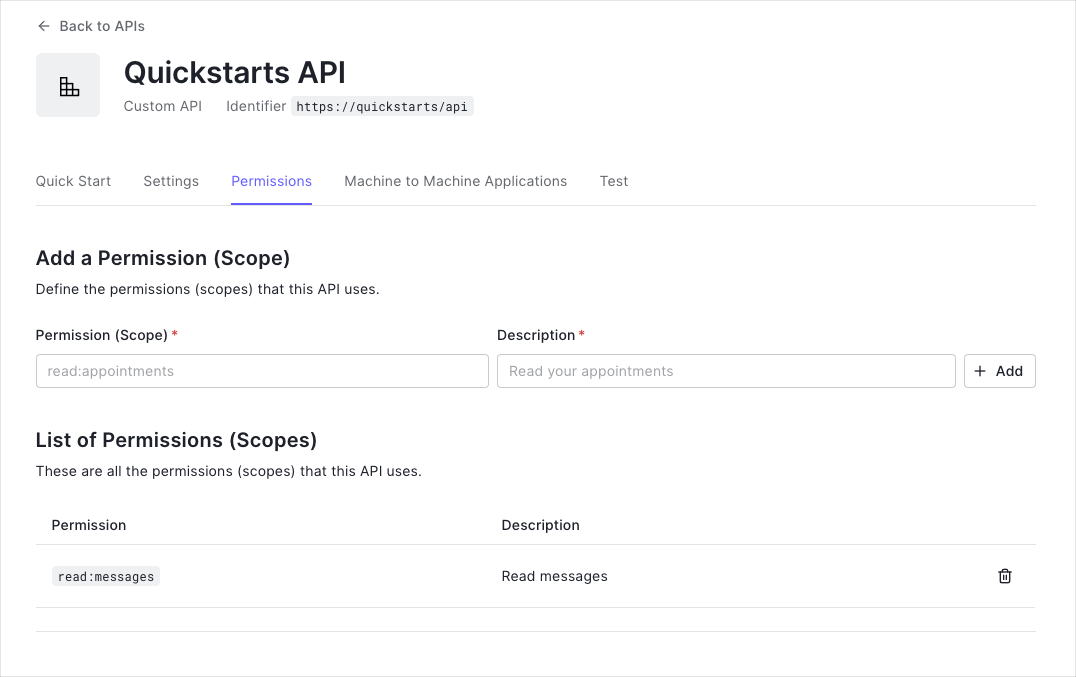
Define permissions
Permissions let you define how resources can be accessed on behalf of the user with a given access token. For example, you might choose to grant read access to the messages resource if users have the manager access level, and a write access to that resource if they have the administrator access level.
You can define allowed permissions in the Permissions view of the Auth0 Dashboard's APIs section.
This example demonstrates:
-
How to check for a JSON Web Token (JWT) in the
Authorizationheader of an incoming HTTP request. -
How to check if the token is valid, using the JSON Web Key Set (JWKS) for your Auth0 account. To learn more about validating Access Tokens, see Validate Access Tokens.
Validate Access Tokens
Download dependencies
Add a go.mod file to list all the dependencies to be used.
// go.mod
module 01-Authorization-RS256
go 1.16
require (
github.com/auth0/go-jwt-middleware/v2 v2.0.0
github.com/joho/godotenv v1.4.0
)Was this helpful?
Download dependencies by running the following shell command:
go mod downloadWas this helpful?
Configure your application
Create a .env file within the root of your project directory to store the app configuration, and fill in the
environment variables:
# The URL of our Auth0 Tenant Domain.
# If you're using a Custom Domain, be sure to set this to that value instead.
AUTH0_DOMAIN='{yourDomain}'
# Our Auth0 API's Identifier.
AUTH0_AUDIENCE='YOUR_API_IDENTIFIER'Was this helpful?
Create a middleware to validate Access Tokens
Access Token validation will be done in the EnsureValidToken middleware function which can be applied to any
endpoints you wish to protect. If the token is valid, the resources which are served by the endpoint can be released,
otherwise a 401 Authorization error will be returned.
Setup go-jwt-middleware middleware to verify Access Tokens from incoming requests.
// middleware/jwt.go
package middleware
import (
"context"
"log"
"net/http"
"net/url"
"os"
"time"
"github.com/auth0/go-jwt-middleware/v2"
"github.com/auth0/go-jwt-middleware/v2/jwks"
"github.com/auth0/go-jwt-middleware/v2/validator"
)
// CustomClaims contains custom data we want from the token.
type CustomClaims struct {
Scope string `json:"scope"`
}
// Validate does nothing for this example, but we need
// it to satisfy validator.CustomClaims interface.
func (c CustomClaims) Validate(ctx context.Context) error {
return nil
}
// EnsureValidToken is a middleware that will check the validity of our JWT.
func EnsureValidToken() func(next http.Handler) http.Handler {
issuerURL, err := url.Parse("https://" + os.Getenv("AUTH0_DOMAIN") + "/")
if err != nil {
log.Fatalf("Failed to parse the issuer url: %v", err)
}
provider := jwks.NewCachingProvider(issuerURL, 5*time.Minute)
jwtValidator, err := validator.New(
provider.KeyFunc,
validator.RS256,
issuerURL.String(),
[]string{os.Getenv("AUTH0_AUDIENCE")},
validator.WithCustomClaims(
func() validator.CustomClaims {
return &CustomClaims{}
},
),
validator.WithAllowedClockSkew(time.Minute),
)
if err != nil {
log.Fatalf("Failed to set up the jwt validator")
}
errorHandler := func(w http.ResponseWriter, r *http.Request, err error) {
log.Printf("Encountered error while validating JWT: %v", err)
w.Header().Set("Content-Type", "application/json")
w.WriteHeader(http.StatusUnauthorized)
w.Write([]byte(`{"message":"Failed to validate JWT."}`))
}
middleware := jwtmiddleware.New(
jwtValidator.ValidateToken,
jwtmiddleware.WithErrorHandler(errorHandler),
)
return func(next http.Handler) http.Handler {
return middleware.CheckJWT(next)
}
}Was this helpful?
By default, your API uses RS256 as the algorithm for signing tokens. Since RS256 uses a private/public keypair, it verifies the tokens against the public key for your Auth0 account. The public key is in the JSON Web Key Set (JWKS) format, and can be accessed here.
Protect API Endpoints
To protect individual routes, pass middleware (defined above) to the http route.
// main.go
package main
import (
"log"
"net/http"
"github.com/joho/godotenv"
"01-Authorization-RS256/middleware"
)
func main() {
if err := godotenv.Load(); err != nil {
log.Fatalf("Error loading the .env file: %v", err)
}
router := http.NewServeMux()
// This route is always accessible.
router.Handle("/api/public", http.HandlerFunc(func(w http.ResponseWriter, r *http.Request) {
w.Header().Set("Content-Type", "application/json")
w.WriteHeader(http.StatusOK)
w.Write([]byte(`{"message":"Hello from a public endpoint! You don't need to be authenticated to see this."}`))
}))
// This route is only accessible if the user has a valid access_token.
router.Handle("/api/private", middleware.EnsureValidToken()(
http.HandlerFunc(func(w http.ResponseWriter, r *http.Request) {
// CORS Headers.
w.Header().Set("Access-Control-Allow-Credentials", "true")
w.Header().Set("Access-Control-Allow-Origin", "http://localhost:3000")
w.Header().Set("Access-Control-Allow-Headers", "Authorization")
w.Header().Set("Content-Type", "application/json")
w.WriteHeader(http.StatusOK)
w.Write([]byte(`{"message":"Hello from a private endpoint! You need to be authenticated to see this."}`))
}),
))
log.Print("Server listening on http://localhost:3010")
if err := http.ListenAndServe("0.0.0.0:3010", router); err != nil {
log.Fatalf("There was an error with the http server: %v", err)
}
}Was this helpful?
Validate scopes
The middleware above verifies that the Access Token included in the request is valid; however, it doesn't yet include
any mechanism for checking that the token has the sufficient scope to access the requested resources.
Create a function to check and ensure the Access Token has the correct scope before returning a successful response.
// 👆 We're continuing from the steps above. Append this to your middleware/jwt.go file.
// HasScope checks whether our claims have a specific scope.
func (c CustomClaims) HasScope(expectedScope string) bool {
result := strings.Split(c.Scope, " ")
for i := range result {
if result[i] == expectedScope {
return true
}
}
return false
}Was this helpful?
Use this function in the endpoint that requires the scope read:messages.
// 👆 We're continuing from the steps above. Append this to your main.go file.
func main() {
// ...
// This route is only accessible if the user has a
// valid access_token with the read:messages scope.
router.Handle("/api/private-scoped", middleware.EnsureValidToken()(
http.HandlerFunc(func(w http.ResponseWriter, r *http.Request) {
// CORS Headers.
w.Header().Set("Access-Control-Allow-Credentials", "true")
w.Header().Set("Access-Control-Allow-Origin", "http://localhost:3000")
w.Header().Set("Access-Control-Allow-Headers", "Authorization")
w.Header().Set("Content-Type", "application/json")
token := r.Context().Value(jwtmiddleware.ContextKey{}).(*validator.ValidatedClaims)
claims := token.CustomClaims.(*middleware.CustomClaims)
if !claims.HasScope("read:messages") {
w.WriteHeader(http.StatusForbidden)
w.Write([]byte(`{"message":"Insufficient scope."}`))
return
}
w.WriteHeader(http.StatusOK)
w.Write([]byte(`{"message":"Hello from a private endpoint! You need to be authenticated to see this."}`))
}),
))
// ...
}Was this helpful?
In this example, only the read:messages scope is checked. You may want to extend the HasScope function or make it
a standalone middleware that accepts multiple scopes to fit your use case.